Splunk Basics - Did you SIEM?
This is a walkthrough for the TryHackMe room Splunk Basics - Did you SIEM?. This room focuses on:

- ingest and interpret custom log data in Splunk
- create and apply custom field extractions
- use Search Processing Language (SPL) to filter and refine search results
- conduct an investigation within Splunk to uncover key insights
The Story 🎅

It’s almost Christmas in Wareville, and the team of The Best Festival Company (TBFC) is busy preparing for the big celebration. Everything is running smoothly until the SOC dashboard flashes red. A ransom message suddenly appears:
The message comes from King Malhare, the jealous ruler of HopSec Island, who’s tired of Easter being forgotten. He’s sent his Bandit Bunnies to attack TBFC’s systems and turn Christmas into his new holiday, EAST-mas.
With McSkidy missing and the network under attack, the TBFC SOC team will utilize Splunk to determine how the ransomware infiltrated the system and prevent King Malhare’s plan from being compromised before Christmas.
Information Gathering
Start the machine and use the IP address 10.82.188.15 for the room to access to the Splunk instance:
https://10-82-188-15.reverse-proxy.cell-prod-eu-west-1c.vm.tryhackme.com
What is the attacker IP found attacking and compromising the web server?
We get the attacker IP by using search query and use field client_ip to find the IP with most events:
index=main sourcetype=web_traffic
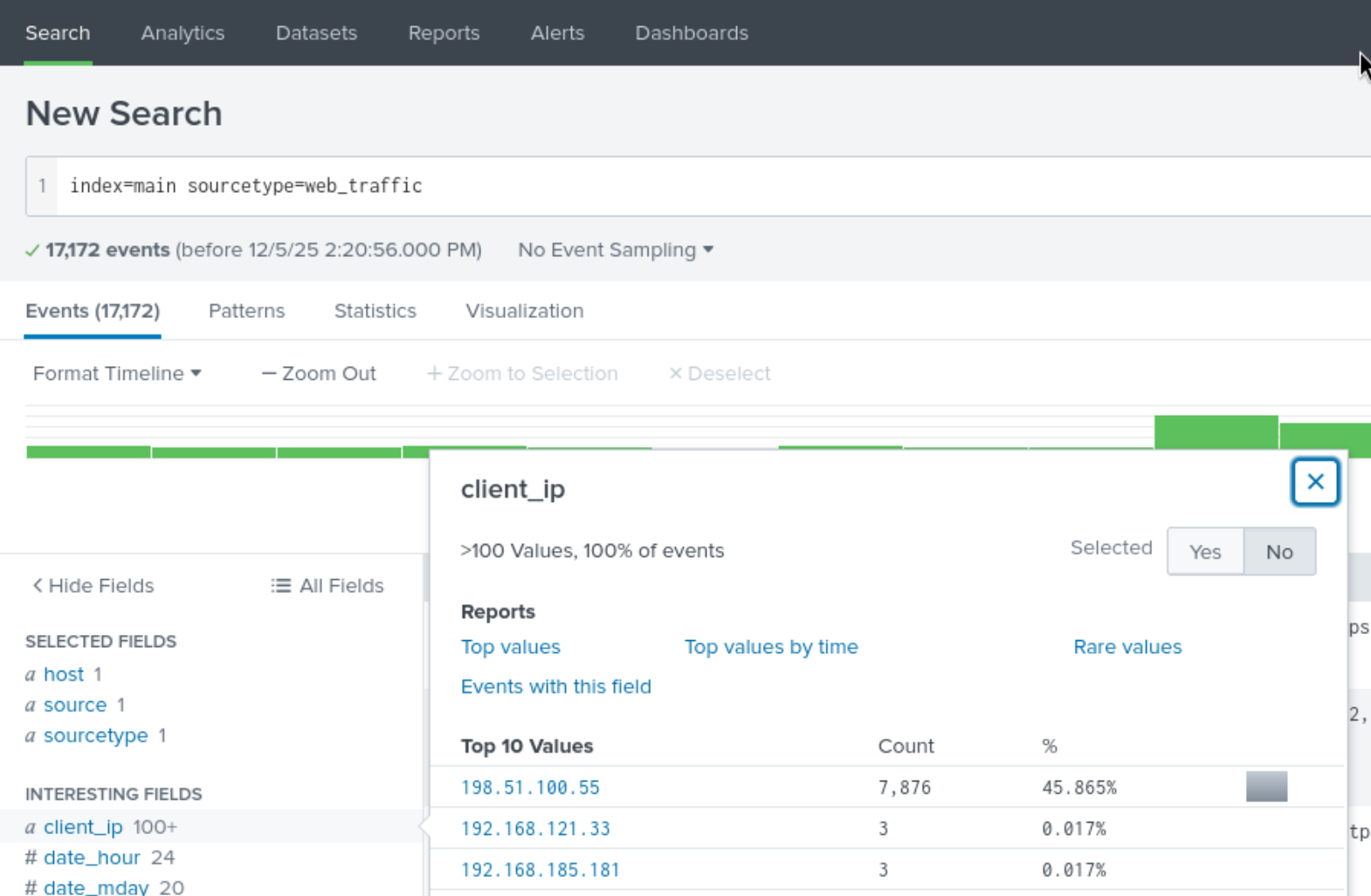
Answer: 198.51.100.55
Which day was the peak traffic in the logs? (Format: YYYY-MM-DD)
We get the peak traffic day by using search query:
index=main sourcetype=web_traffic | timechart span=1d count | sort by count | reverse
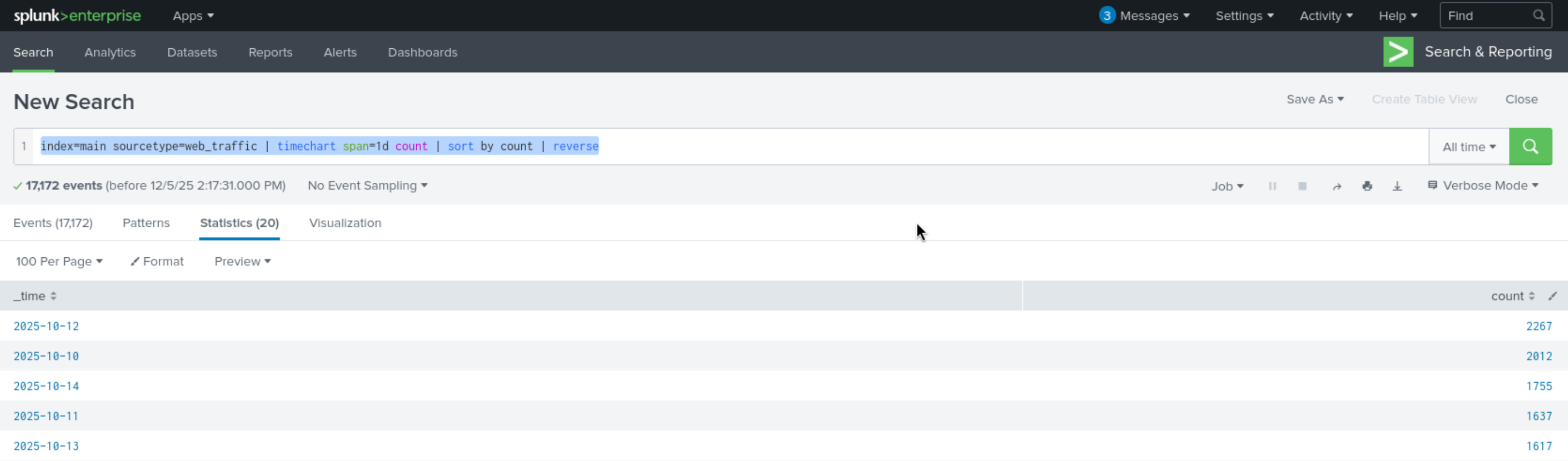
Answer: 2025-10-12
What is the count of Havij user_agent events found in the logs?
We get the count of Havij user_agent events by acessing field user_agent.
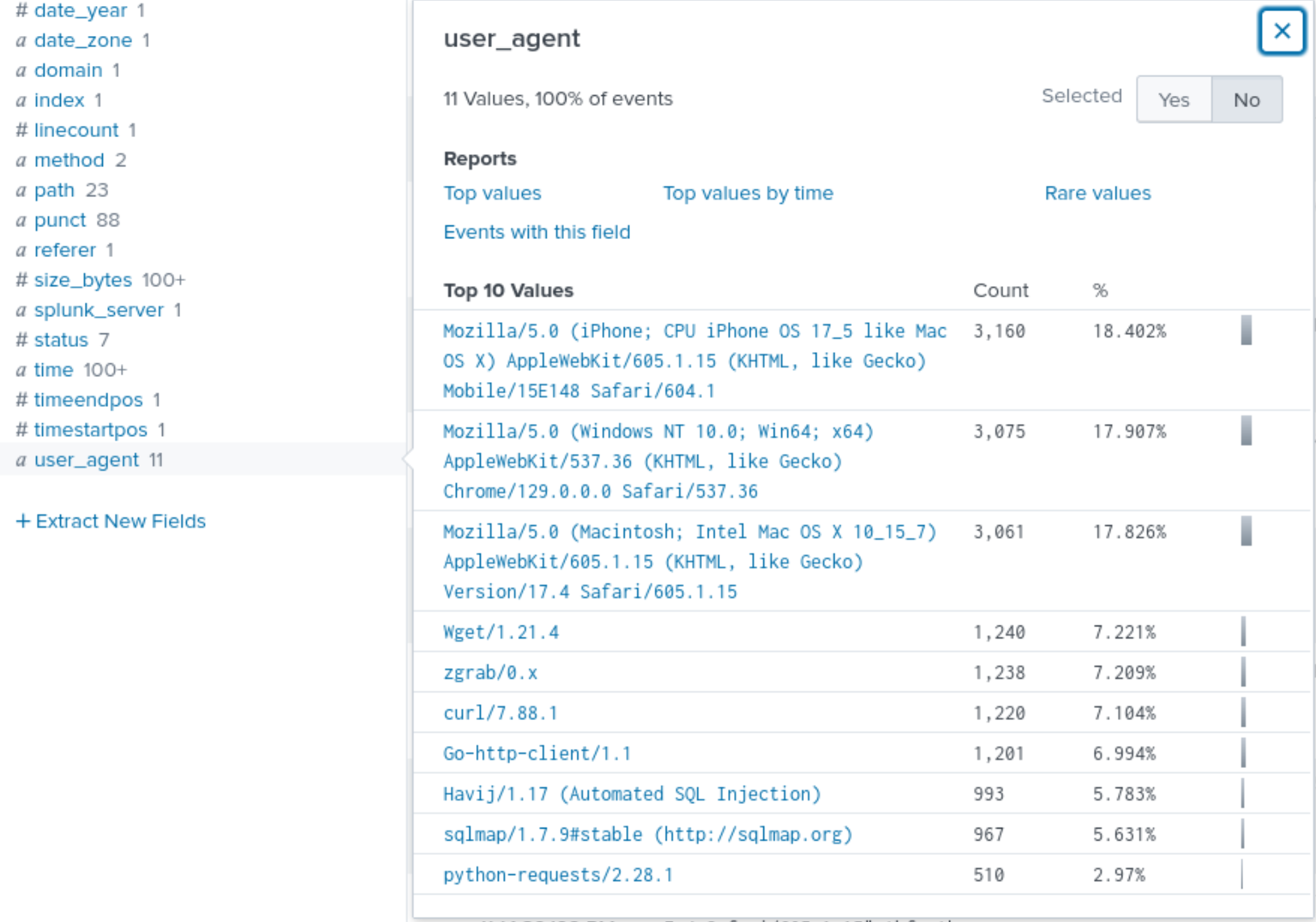
Answer: 993
How many path traversal attempts to access sensitive files on the server were observed?
We get the count of path traversal attempts by searching for common path traversal patterns in the path field:
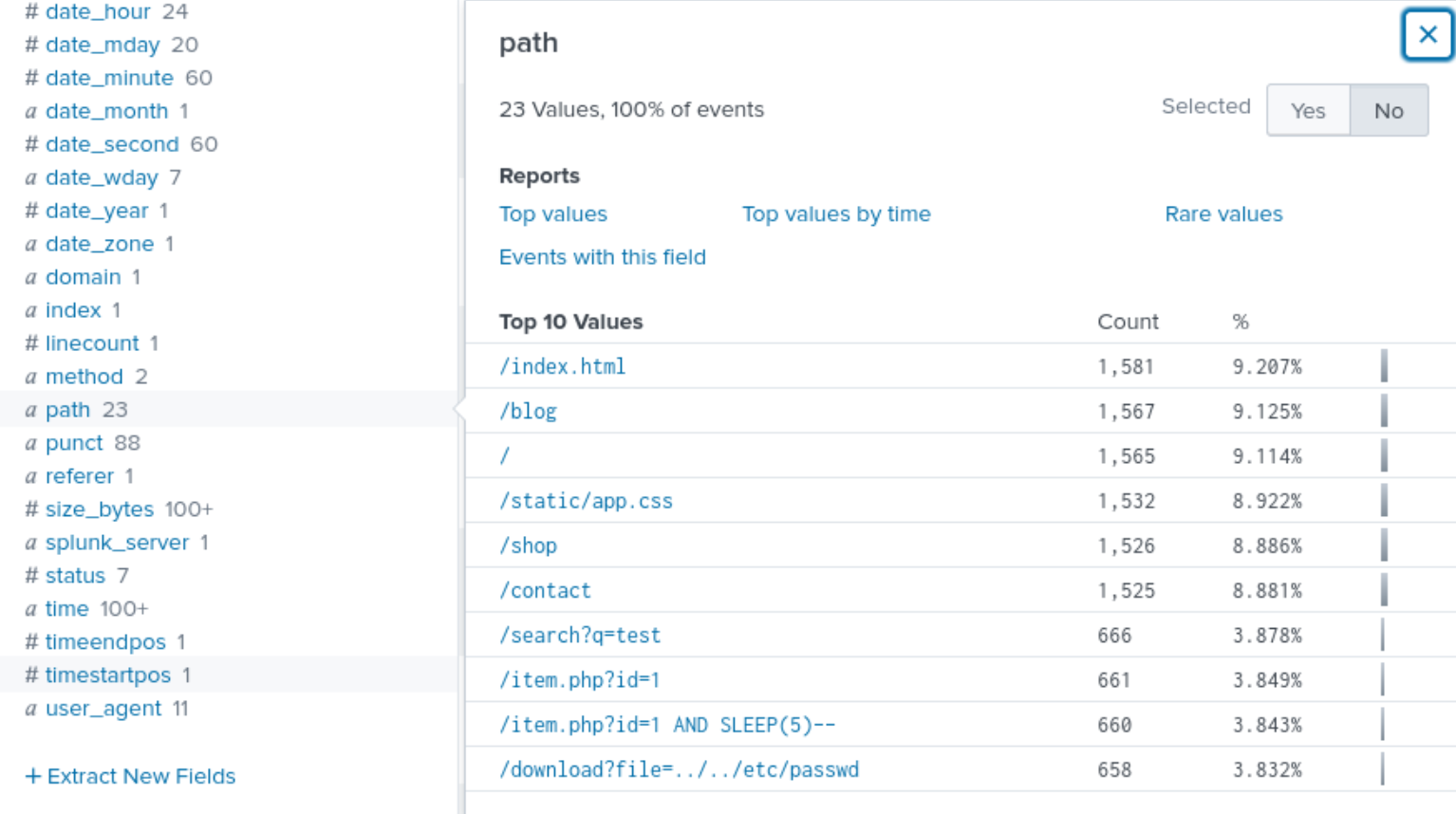
Answer: 658
Examine the firewall logs. How many bytes were transferred to the C2 server IP from the compromised web server?
To get the bytes transferred to the C2 server IP, we filter the firewall logs for the C2 server IP:
sourcetype=firewall_logs src_ip="10.10.1.5" AND dest_ip="<REDACTED>" AND action="ALLOWED" | stats sum(bytes_transferred) by src_ip
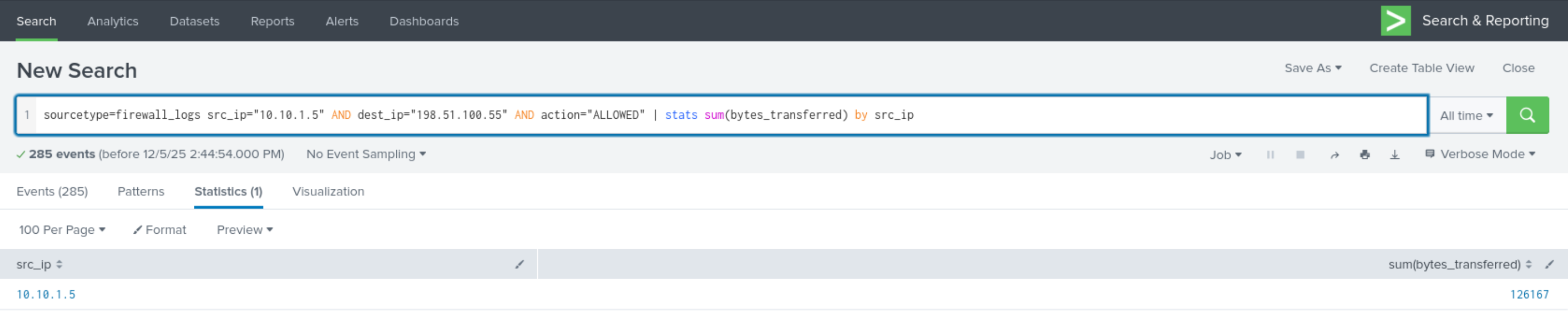
Answer: 126167
Completion
This was a fun introduction to Splunk basics and log analysis. I learned how to ingest and interpret custom log data, create and apply custom field extractions, use Search Processing Language (SPL) to filter and refine search results, and conduct an investigation within Splunk to uncover key insights.